An Overview of Fraud and Cybersecurity

Protecting against the threats and attacks that fraud and cybersecurity pose is an ever-increasing concern for businesses today. For many, it has become imperative to safeguard their organizations from such dangers.
We have all seen the figures placed on the cost of fraud and cyberattacks to businesses and the economy with the projected costs to reach $2 trillion by 2019. Less sensational than its financial implications, though, but far more disruptive, are the reputational damage and the business impact that arise in the aftermath of successful attacks.
Protecting against the threats and attacks that fraud and cybersecurity pose is an ever-increasing concern for businesses today. For many, it has become imperative to safeguard their organisations from such dangers, especially considering that threats and attacks are continuing unabated as the methods of fraudsters and attackers evolve and change to reach their ends.
Available data indicates that instances of fraud and cybersecurity attacks are increasing not just in frequency but in severity and impact. Companies that fail to ensure that their employees are fully trained to recognise and tack action against this using adequate security processes, procedures and protocols, therefore, not only face a greater risk of financial loss, which includes loss of assets, but a greater risk of reputational damage and business disruption, which includes negative publicity.
How has the fraud landscape changed?
Fraud and cybersecurity threats continue to evolve as better organised and more sophisticated attackers have emerged. As illustrated in diagram 1, fraudsters and cyber attackers have become much more sophisticated in recent years. There has been a noticeable shift in the profile of those behind attacks.
In the past, attackers were primarily individuals operating on an opportunistic, casual or ad hoc basis, largely driven by the desire to prove that they could successfully carry out a fraud attack.
Acting alone or in collusion to commit internal or external fraud, fraudsters increasingly perpetrate acts that are focused on disruption and destruction.
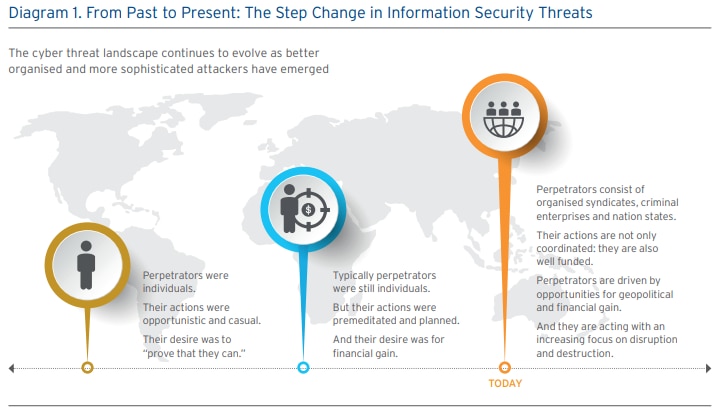
Today, attackers are highly organised syndicates and criminal enterprises that are managed in a similar way to businesses. These criminal enterprises are typically well organised and, importantly, well funded. Their motives are primarily for financial gain but in some instances for geopolitical gain. These fraudsters are also increasingly focused on disruption and destruction. There is also the risk of internal fraud and similarly internal fraud may be undertaken by an opportunistic individual or by an employee who operates in collusion with an organised criminal group.
Diagram 2 shows the changing nature of the various aspects of a fraud or cybersecurity attack. Most notably, attacks are becoming increasingly targeted with fraudsters undertaking a large amount of research and planning prior to attempting an attack. Attempted attacks have also moved from a pattern of one-off, opportunistic attacks to targeted, planned and continuous attacks. Attackers will continue their attempts on one target if there is a chance of success.
Attack methods are also continuously evolving and adapting to overcome the defences that organisations create. Unsurprisingly, there has been a growth in the use of technology by fraudsters. Attack methods tend to target weaknesses in technology and in human nature and in some instances both. It is for this reason that it is so important to frequently review internal procedures and processes and to ensure that all employees are fully trained and aware of their responsibilities in the event of an attempted attack.



